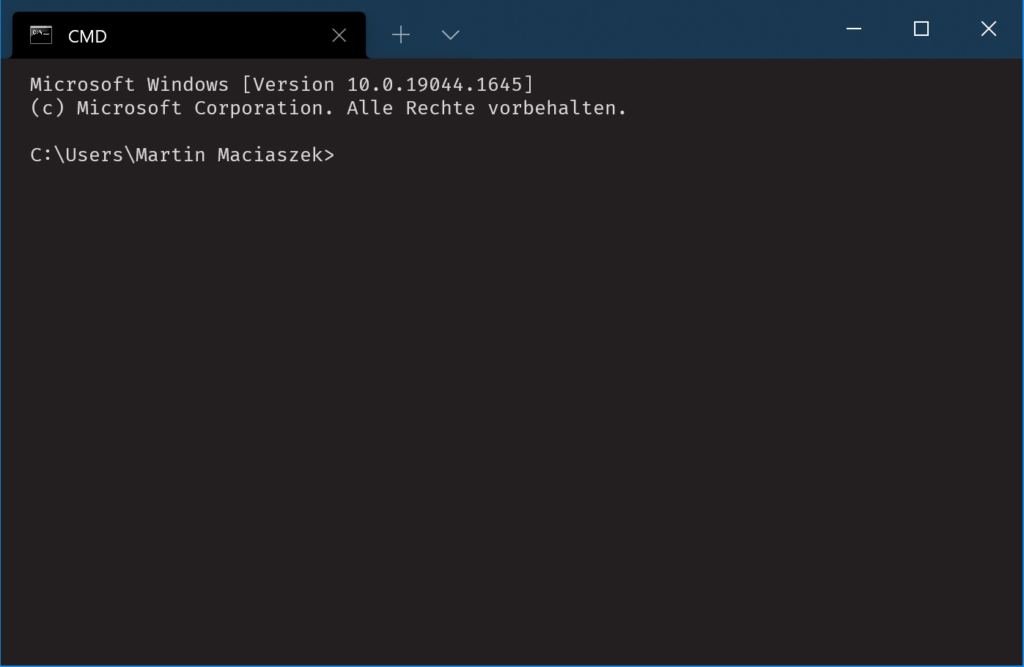
Install a Python development environment on Windows
2023-10-27: Updated to use pipx and now manual PATH fiddling. I was trying to set up a Windows-native Python development environment with Poetry. Since Microsoft is doing a lot of Python extensions for VSCode I expected this to be a breeze. Well… there are some stumbling blocks along the way. Anyway, here’s how I got…
Programmer’s Utilities Guide recreation

After recreating the CP/M User’s Guide, then the CP/M Programmer’s Guide, and the CP/M System Guide I thought I would be done. But then the System Guide referenced yet another Guide: the Programmer’s Utilities Guide. For now this will be the last of my Digital Research manual recreations. This guide is based on this scan…
CP/M System Guide recreation

This is the third part of my CP/M manual recreation project. After recreating the CP/M User’s Guide, and then the CP/M Programmer’s Guide, this is now the System Guide. Like with the previous two recreations, I based this on the OCRed version of the CP/M System Guide. Files CP/M System Guide (interactive PDF with hyperlinks…
CP/M Programmer’s Guide recreation

This is the second part of my CP/M manual recreation project. After recreating the CP/M User’s Guide first, this is now the Programmer’s Guide. As with the first part, I based my recreation on the OCRed versions on the OCRed version of the CP/M Programmers’s Guide. Files CP/M Programmers’s Guide (interactive PDF with hyperlinks for…
JiffyDOS User’s Manual

Sometime in 2016 I recreated the JiffyDOS User’s Manual in InDesign. This was just an excercise to get more comfortable with InDesign. Long story short, here is the result: JiffyDOS 6 Users Manual (interactive PDF version for online reading) JiffyDOS 6 Users Manual (print-ready version with crop marks) Use them for good, not for evil.
CP/M User’s Manual recreation

My original CP/M manuals are starting to fall apart. There are scanned and OCRed versions of these manuals available on the internet but these look plain and contain errors that were introduced by OCR. Based on the OCRed version of the CP/M User’s Manual I tried to faithfully recreate the old manual. The resulting PDFs…
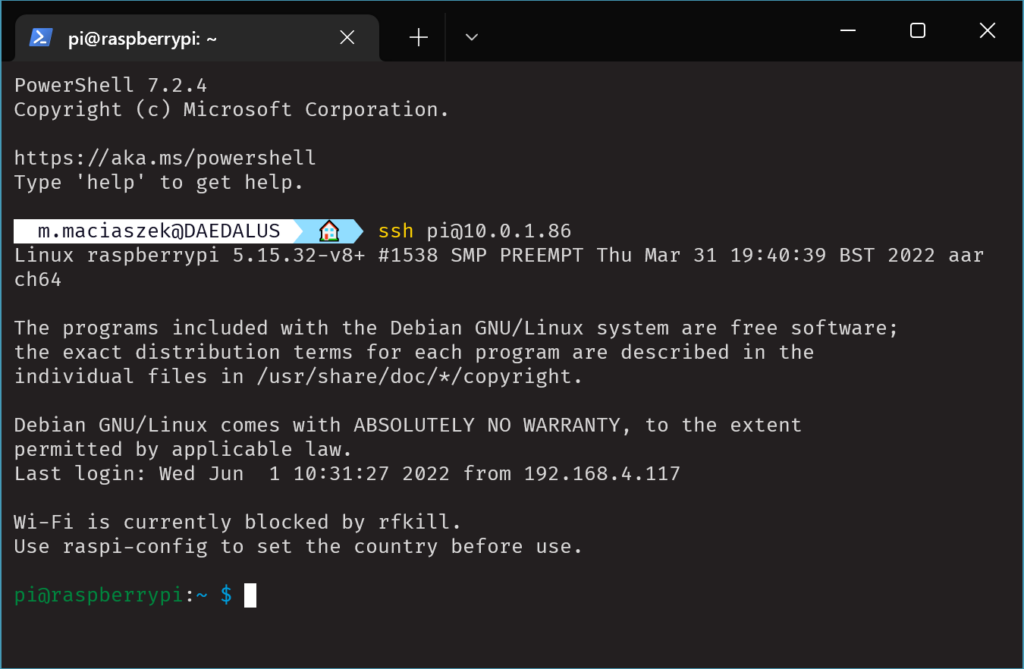
SSH on Windows

You’ve mastered all the SSH settings on your Linux/Mac and suddenly you’re thrust into the Windows world and need to access another machine via SSH. Old-school Windows users will probably download PuTTY. That should allow the most basic SSH operations. But once you need to do some more advanced stuff, you’ll also need to download…
Use Windows Terminal by default

Have you ever thought that the default Windows console host is a clunky old piece of garbage? Choosing the font or colors is awkward at best. And it can’t be even resized horizontally. What a piece of crap! Microsoft seems to have finally realized that and started the Windows Terminal project. Once you install Windows…
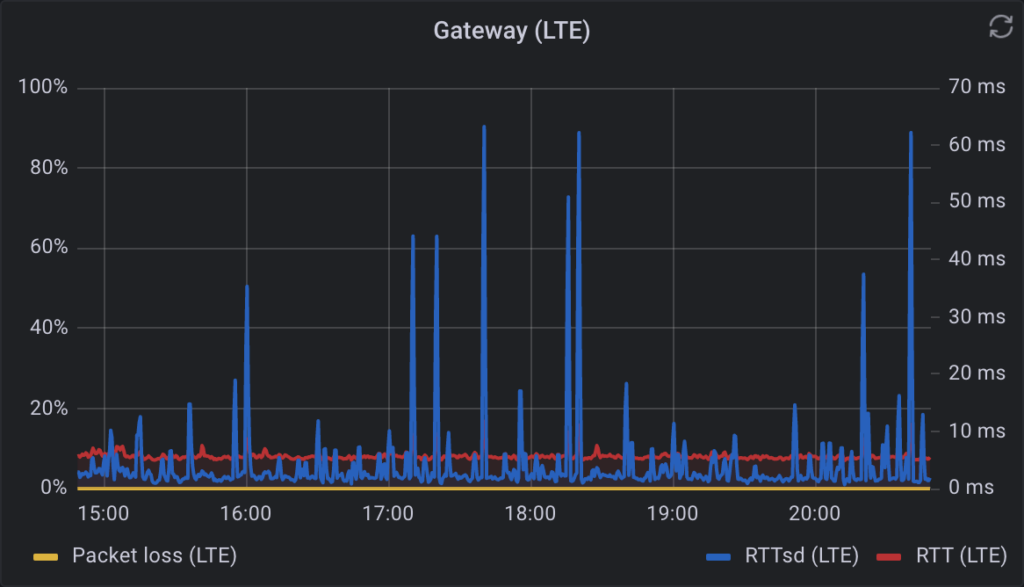
Pfsense Gateway Latency with Telegraf

Some years ago I started using the Telegraf package on pfSense and was disappointed to find out that it didn’t report the gateway latencies. So I wrote a quick&dirty Python 2 script that would parse the output of pfSense’s dpinger and output it in a format that Telegraf could send to InfluxDB. With the most…